













Study with the several resources on Docsity

Earn points by helping other students or get them with a premium plan


Prepare for your exams
Study with the several resources on Docsity

Earn points to download
Earn points by helping other students or get them with a premium plan
Community
Ask the community for help and clear up your study doubts
Discover the best universities in your country according to Docsity users
Free resources
Download our free guides on studying techniques, anxiety management strategies, and thesis advice from Docsity tutors
An in-depth exploration of secure software development, focusing on the application of touchpoints such as requirement and use cases, architecture and design, test plans, code tests and test results, feedback from the field, and abuse cases. It also covers security requirements, risk analysis, and the use of secureuml for role-based access control and mandatory access control. The advantages and limitations of model-driven software development integrated with security, as well as the importance of formal semantics for security considerations.
Typology: Slides
1 / 39

This page cannot be seen from the preview
Don't miss anything!












Requirement and Use cases
Architecture and Design Test Plans^ Code^
Tests and Test Results
Feedback from the Field
5. Abuse cases 6. Security Requirements 2. Risk Analysis
External Review
4. Risk-Based Security Tests 1. Code Review (Tools) 2. Risk Analysis 3. Penetration Testing 7. Security Operations
Source: Wikipedia, http://en.wikipedia.org/wiki/Unified_Modeling_Language
Users
Roles
Permissions
Sessions
User assignment
Permission assignment
Constraints
Lecture 17^13
Mandatory Access Control Security Labels: (A,C) , where A: total order, e.g., Top-Secret > Secret > Public C: domain (subset), e.g., subsets of the set {5, 7} are: {5,7}, {5}, {7}, {} and {5,7} ⊇ {5,7}|{5}|{7}|{}, {5} ⊇{5}|{}, {7}⊇{7}|{}, {} ⊇{} but {7} NOT ⊇ {5} Dominance (≥): label l=(A,C) dominates l’=(A’,C’) iff A ≥ A’ and C ⊇ C’ e.g., (confidential,{student-info}) ≥ (public,{student-info}) BUT
(confidential, {student-info}) NOT ≥ (public,{student-info, department-info})
Lecture 17^14
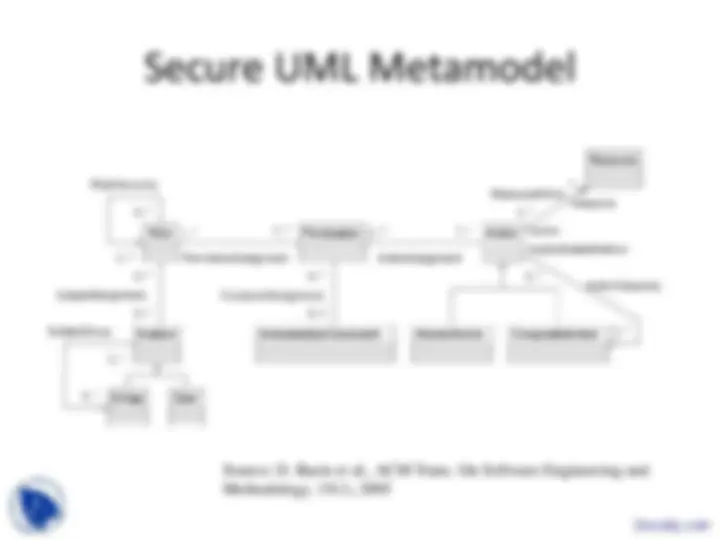
Source: D. Basin et a., ACM Trans. On Software Engineering and Methodology, 15(1), 2005
Source: D. Basin et a., ACM Trans. On Software Engineering and Methodology, 15(1), 2005